 I’m amazed how much bad practice there is around security. People just aren’t very good at it, and sometimes don’t even realize that there is a security issue to worry about. It is not just that people aren’t good at it; they think they are.
I’m amazed how much bad practice there is around security. People just aren’t very good at it, and sometimes don’t even realize that there is a security issue to worry about. It is not just that people aren’t good at it; they think they are.
Here’s one example. When I was an undergraduate in 1974 it was already standard practice in operating systems to store passwords after processing them through what was then called a one-way cipher and would today be called a hash function. Yet today, if you forget your password, many websites will simply send you an email telling you what it is (as opposed to resetting it and telling you what they reset it to). This is bad for so many reasons. Firstly, it should never be stored unhashed in the database since it risks the entire database being stolen (and thus everyone’s passwords). Since email is not secure, sending a password through email risks it being compromised that way. And you should not have your password on your computer anywhere (such as in an email) since one way of optimizing password search is to try every word on a person’s computer, orders of magnitude quicker than an exhaustive search. So something that was being taught to undergraduates nearly 40 years ago is still not being done.
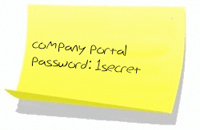
That’s before worrying about the real weak link in security: users. We are all exhorted to have long passwords, not contain words, change them regularly, use different passwords for different purposes and so on. Nobody does that. What almost everyone does is have one weak password for stuff you don’t care about (if you really want to read the New York Times while pretending to be me then be my guest) and a stronger one for things you care a lot about (if you want access to my bank account then definitely don’t be my guest). Often banks insist on strong passwords (must contain an upper case letter, a lower case letter and a digit for example). So lots of people just write it down and stick a post-it on the computer. But then the usual set of backup questions are required for users who forget their passwords. I just don’t think it is that hard for someone to find the last 4 digits of my social security number and my mother’s maiden name (and an amusing aside: one website wouldn’t accept the answer to my mother’s maiden name question since it only has 4 characters and was deemed too short! It wasn’t even Wu or Li). It was a password recovery weak link that led to all the Twitter documents being compromised a few weeks ago.
As Bruce Schneier says, amateurs attack the cryptography; professionals attack the people. It’s even got a name, social engineering. Most readers of this blog are tech savvy and are at least suspicious of things like emails that look like they are from your bank or Paypal requiring you to go and log in. We are aware that the site you end up on might look like Paypal but probably is some password harvesting site. But less tech savvy people haven’t a chance. They’ve never heard the term phishing and don’t have any feel for which emails might be genuine and which are clearly fraud.
When people are phoned up they are even more vulnerable. There’s a lovely story of some high-up general inside the Pentagon saying that his password would be impossible for anyone to get. Susan Headley, a famous social engineer who had been briefing these generals, picked up the phone, pretended to be an admin in the Pentagon, called the general’s admin back wherever he was based and said the general had forgotten his password. She had it in a minute. But think about it. The general’s admin knew he was at the Pentagon, caller-ID may even have confirmed that, and so the whole story somewhat checked out.
A couple of years ago (I can’t find the reference any more) a security company went to a tradeshow, picked up lots of free USB memory sticks, loaded them up with a “phone home” program and then scattered them in the parking lots outside big companies. Well over half the memory sticks were inserted into computers inside the firewalls of those companies. If you found a memory stick beside your car are you sure you’d destroy it or might you see if it is any good (especially a couple of years ago before they became dirt cheap)?
Memory sticks are prohibited inside the DoD and homeland security since they became a vector for malware getting from employee’s home computers inside the firewall. Apparently this causes huge problems for some people since the DoD has many disconnected networks ("airgapped") and USB sticks were the way data got transferred between them. On coastguard ships there is equipment that doesn’t have a CD reader and without a USB stick, no way to update its tables.
One mail I can’t work out is that almost every day I get an email telling me I’m being sent a billing summary for my records, which is attached. But there is no attachment. I’m sure it is some sort of phishing attack but I guess somewhere along the email chain the attachment got stripped off for being too suspicious.
